Followup: Some Reddit readers tackled this challenge and conquered it. Read up on it here.
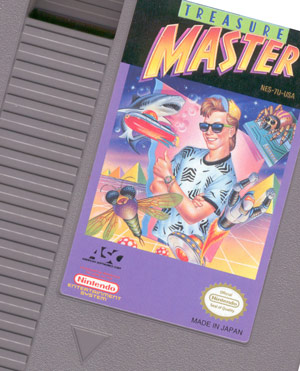
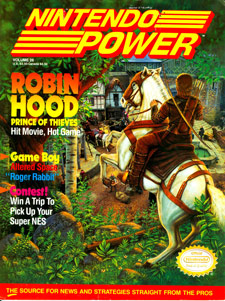
Back in the glory days of the old 8-bit Nintendo Entertainment System, I used to read my Nintendo Power magazine issues religiously. One issue that stood out to me, and that I never forgot about, is one that briefly mentioned Treasure Master (volume 26, July 1991, Robin Hood: Prince of Thieves issue).
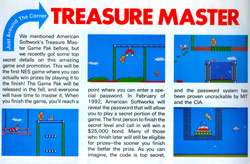
This will be the first NES game where you can actually win prizes by playing it to the finish! The Game Pak will be released in the fall, and everyone will have time to master it. When you finish the game, you’ll reach a point where you can enter a speical password. In February of 1992, American Softworks will reveal the password that will allow you to play a secret portion of the game. The first person to finish the secret level and call in will win a $25,000 bond. Many of those who finish later will still be eligible for prizes– the sooner you finish, the better the prize. As you can imagine, the code is top secret, and the password system has been proven uncrackable by MIT and the CIA. (emphasis added)
|
 click for larger image |
So the gimmick for this substandard, side-scrolling, run & jump game was that players would buy it, play it, and build up skill in a few months. Then, after everyone has had a chance to get really good at the game, the company would release a password that would unlock a secret stage. Play through this stage and you could win big prizes.
Naturally, the part about the uncrackable code caught my attention. I didn’t even realize the CIA provided such a vetting service. Anyway, I didn’t hear anything else about the game again. Many years passed and I saw the game in a used video game shop. I figured it was time to revisit the uncrackable code issue since I know a little more about computers and codes now. And I also know better than to accept an uncrackable code claim at face value.
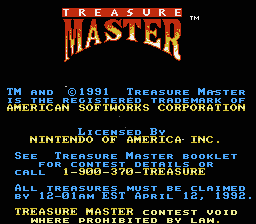
How uncrackable is the code? The introductory blurb from Nintendo Power raises some questions, many of which can be answered by the Treasure Master instruction manual. The full details of the contest are provided. Apparently, the password was to be announced on MTV on April 11, 1992, probably during a commercial. Players would enter the password, along with their game cartridge’s unique serial number, in order to unlock the special levels of the game. Upon completion of the levels, the game would return a special winning number that the player could give to the operator on the other end of a 1-900 phone number to try to win a prize.
To be fair, the official manual doesn’t mention the uncrackable code nonsense. The James Bond material highlighted in the Nintendo Power preview can probably be attributed to some Marketing/PR flunkie at American Softworks working more closely with the magazine than their own engineering department.
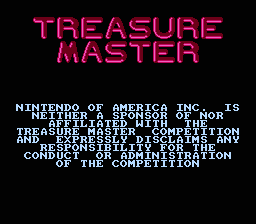
Also, Nintendo really wants you to know that they have nothing to do with the contest:
Threat Model
Continue reading